IEEE std 802.1AR:2009 pdf free download.IEEE STANDARD FOR LOCAL AND METROPOLITAN AREA NETWORKS.
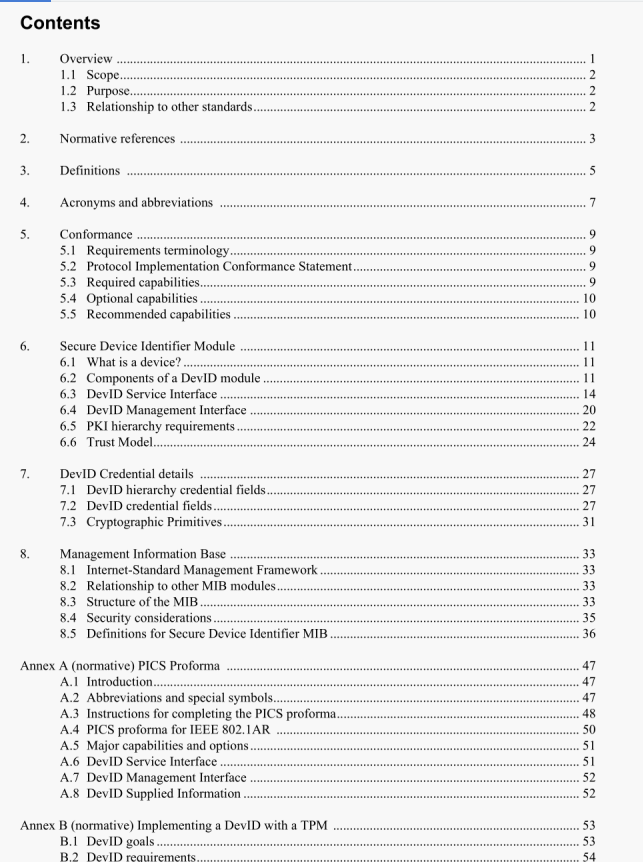
6. Secure Device Identifier Module
This clause describes the logical components of the DeviD Module. It provides the necessary context for understanding the security requirements (and acceptable practical limitations on those requirements) for thc creation, use, maintenance, and dcletion of DcvlD credentials. An overview of DevID credentials is provided although thc details of DcvlD fields are specified in Clause 7 (DcvID Credcntial details).
Informative use cases are provided in Annex C as examples.
6.1 What is a device?
A device is any entity in an IEEE S02 LAN that seeks to obtain services from the network or provide services on the network. A device is defined by having a single l[)evlD credential.
Multiple logical or physical devices may be contained within an aggregate device. Each of these logical or physical devices will have its own unique DeviD. The DevID used to identify the aggregate device may depend on the context under which the identification of the aggregate device is done. The selection of a Dcv ID based on this context is beyond the scope of this document. Service interfaces defined in 6.3 do nOt refer to aggregate devices.
The DevID module is a logical security component that stores and operates on the DevID secrets and associated DevlD credentials. The PIUS shall describe the device the DevID module is identifying.
6.2 Components of a DevID module
The components of a Dcv ID module are shown in Figure 6-1. Implementations may provide additional functionalities. The Dcv ID credential and DeviD secret are used by the DeviD module to prove the identity of the device. It is imperative that the DeviD secret is securely protected from access by any other entity. The DeviD credential is publicly available to any entity that wishes to verify the identity of a device.
6.2.1 DeviD credentials
The Dcv ID module shall include the IDevID and zero or more LDevlDs. At least one LDevlD credential should be supported.
The DevIl) module shall include the entire credential chain up to the root credential and should include the root credential. For a shallow hierarchy this requirement could be met with only the Devil) credential on the device. The root certificates should be shipped along with the device or made available by the solution manufacturer in a reasonably discoverable fashion such as on the manufacturer’s Web site.
The DeviD credential format shall be as described in Clause 7 (DevID Credential details).
IEEE std 802.1AR:2009 pdf free download